This page describes the major phases of the incident response process — preparation, detection and analysis, containment, eradication, recovery, and post-incident activity. It is not meant to substitute for an incident response plan but serve as a general description.
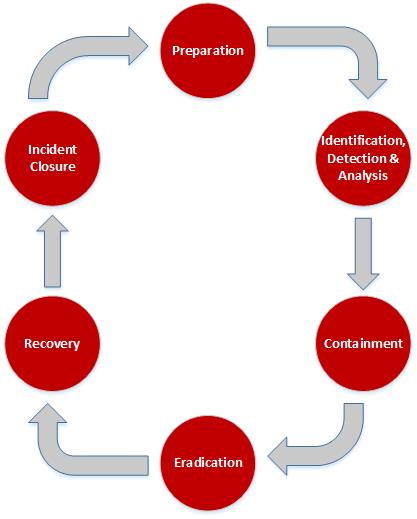
Preparation
Preparation is fundamental to incident response. Incident response methodologies typically emphasize the proactive and ongoing use of tools, training, and processes necessary for preventing incidents by ensuring that systems, networks, and applications are sufficiently secure.
Using the NIST Cybersecurity Framework, and engaging in an IT Risk assessment are recommended preparation practices for Universities, Colleges, and departments. The benefits of conducting an IT Risk assessment including identifying applicable threats. Another benefit is that critical resources are identified, allowing staff to emphasize monitoring and response activities for those resources.
Identification, Detection, and Analysis
Early steps taken to detect, verify, investigate, and analyze an incident are important to developing an effective containment and eradication strategy. Once an incident has been confirmed, resources can be assigned to investigate the scope, impact, and response needed.
Coordination is important to make sure that steps taken to verify the incident do not alter data that will be needed for further investigation.
Containment
Containment procedures attempt to actively limit the scope and magnitude of the attack. Containment involves acquiring, preserving, securing, and documenting all relevant information. Containment has two goals:
- Prevent data from leaving the network via the affected machines.
- Prevent the attacker from causing further damage to information technology assets.
Eradication
Eradication is the removal of malicious code, accounts, or inappropriate access. Eradication also includes repairing vulnerabilities that may have been the root cause of the compromise. The general steps involved in the eradication phase of the incident are to:
- Identify and mitigate all vulnerabilities that were exploited.
- Remove malware, inappropriate materials, and other components.
- If more affected hosts are discovered, repeat the Detection and Analysis phase to identify all other affected hosts, then contain and eradicate the incident for them.
- Reinstall OS, apply patches, reinstall applications, and apply known patches as appropriate.
Recovery
Once the incident has been contained and eradicated, recovery can start. This phase allows business processes affected by the incident to recover and resume operations.
Incident Closure
Documentation of a cyber-incident and the steps taken to mitigate issues encountered are important. The documentation offers an opportunity to improve incident response processes and identify recurring issues. Certain cyber incidents should be documented more thoroughly when their impact warrants.
